Another day, another hacking challenge…
Today’s challenge is to find the password for level 9.
To view level 8, please go HERE.
After entering the username/password we see the following screen:

On the right side there’s a link that says, “view sourcecode”.
Clicking this link we see the following:
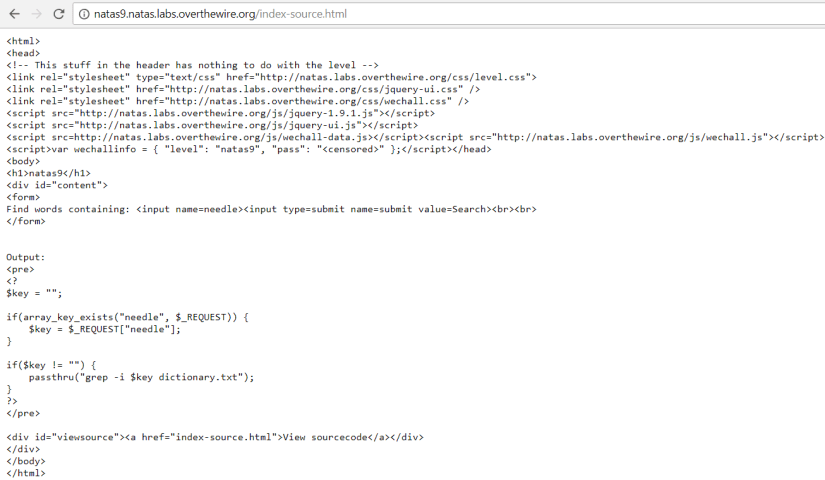
First, you should notice that there is weird syntax (language) of “<? and ?>” What is this? Well, this is PHP (Personal Home Page). Which is a server-side programming language.
What exactly is passthru? Passthru is a function that executes a command. To learn more about the passthru function click HERE. In this case we’re using the word in the first screenshot to look through a file named dictionary.txt.
Let’s try to enter the word “test” to see what we get…

The code returns all of the words that have test in it. OK. Let’s see if we can get ALL of the words in the dictionary.txt file.
Let’s try the word of “” instead of test. Doing that we get the following:

We have all the words in the dictionary.txt file. Why did I pick “” ? Well if you look in the passthru function the command was enclosed in quotes. I figured that if I entered quotes we would break out of the command which would produce all of the words in the file.
So now we have all of the words, what do we do now?
The challenge seems to be vulnerable to command injection. To learn more about command injection, go to the link HERE.
Let’s try to add another command to list all of the directories in the folder. The command to enter is: ls%20-la; (%20 is the URL encoding of space). This command is listing all of the files in the directory include hidden ones (in Linux hidden files start with the “.”).

We have listed all of the directories, and have a potential gem. There’s a file named .htpasswd. Let’s add on to the command sequence to open this file. To do that we add the following: cat%20.htpasswd;.

We have received the password! Which is: $1$p1kwO0uc$UgW30vjmwt4x31BP1pWsV.
















































You must be logged in to post a comment.